In the last few months we have noticed an increase in the amount of scam/ phishing emails. These kinds of emails are constructed by a scammer to try and trick a user into providing personal information such as bank details and passwords. The emails appear to be sent from a legitimate sender.
The quantity of such emails is of course a worry, but in addition to this the quality of these scam emails is alarming. In the early days of phishing it was quite easy to spot a scam email straight away. However, the examples we are seeing nowadays have an incredibly authentic feel to them. Even IT professionals sometimes struggle to identify the difference between a genuine email and a spam email.
Let’s look at some of the recent phishing emails we have encountered this month. Ask yourself if you think you could have been fooled. Be honest!
Telstra Scam Example:
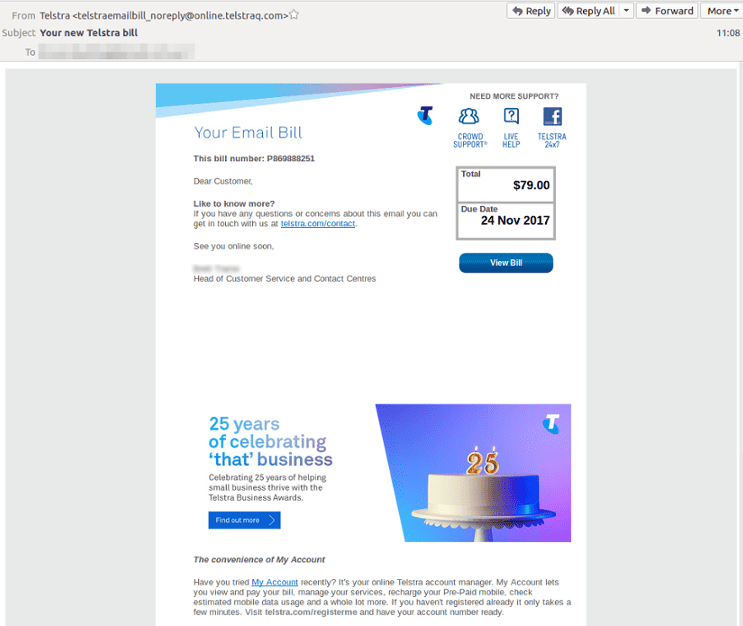
At first glance, this email doesn’t display any obvious signs of being fake. It appears to be a normal phone/ internet bill that one may expect to receive. The document uses official logos and the layout and presentation has been constructed well. The senders display name (‘Telstra’) and the subject header also appear genuine. There are links to actual Telstra webpages which could also make a user feel safe.
The main indicator of a scam email we would look for initially is the sender’s domain. This email has been sent from ‘…@telstraq.com’ and not ‘…@telstra.com’. The inclusion of the ‘q’ is the giveaway but that isn’t too noticeable when browsing over the email quickly.
This email is completely fabricated; however it is incredibly deceiving and difficult to spot it’s not genuine. With scam emails like this one, they will normally contain a link where the user will be asked to enter their details (email and password). The attacker will then have access to this personal data, leaving the user compromised.
This email however has a link that directs the user to a SharePoint page, where they are asked to download a folder. The user may think this folder contains their phone bills, but actually contains malicious files. These files can automatically download malware onto their computer.
Netflix Scam Example:

Just like with the preceding Telstra example, this email looks perfectly normal. The logos appear as one would expect and so is the font. It could be easy to be duped by this scam. The purpose of this email is to convince a user that their payment for Netflix has bounced and so they need to update their bank details.
When you click on ‘Restart Membership’, you are taken to the below website. Look at the below two images. One is the genuine Netflix login page, one is a scam webpage. Spot the difference!
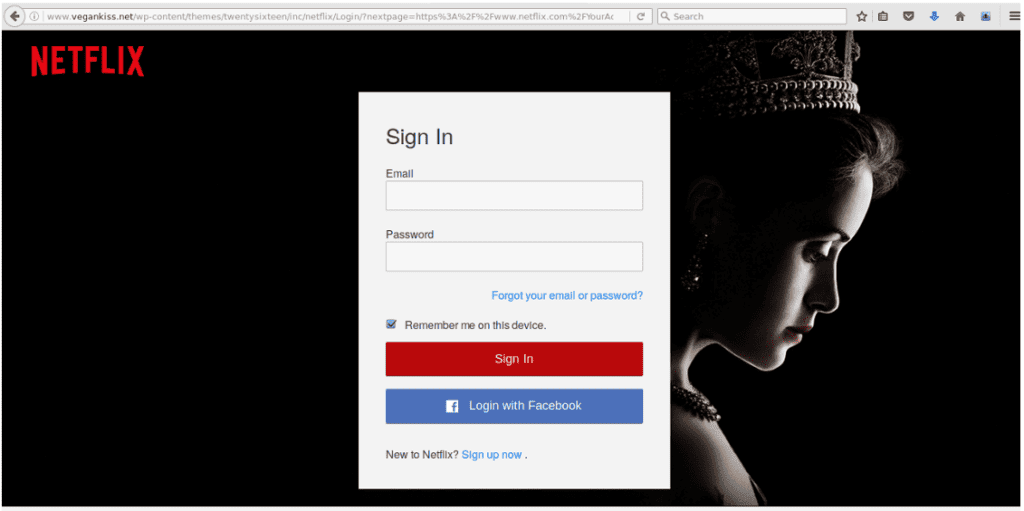

Did you guess the first webpage is the scam one?
There are some noticeable differences, but would you have picked them out if you didn’t have the actual Netflix webpage in front of you to compare?
Just like when we checked the sender’s domain for the Telstra example, check the website domain for the scam webpage. The domain is ‘vegankiss.net’, not ‘netflix.com’. This is the giveaway.
If you were in a rush to see a newly released TV series (Stranger Things anyone?), would you have quickly entered your details without checking for any hazardous signs?
Take Home Message:
Scammers are getting smarter! Don’t become the latest victim!
In all aspects of computing and technology, it is useful and beneficial to stay ahead of the game. Keep yourself educated and always proceed with caution. In terms of cyber-security, questioning everything is not the worst mindset to have.
We will be following up this blog shortly with an article highlighting the factors you should look out for when analyzing emails for potential scam.
If you can’t wait for the next blog and you’re in desperate need of some mail protection, speak to one of our security specialists today on 1300 770035 or email security@bangitsolutions.com.

