Email scams never stop and neither do we! For the month of September there are two more scams that have popped up on MailGuard’s radar that you should be aware of.
The first one involves using Adobe Document Cloud to harvest a user’s credentials and the second scam is a Zoom-like phishing email.
Adobe Document Cloud
This Adobe phishing scam sees an email looking like it’s from Adobe Document Cloud, which could be the latest attempt in scamming user’s sensitive data.
Sent from ‘Document via Adobe Acrobat’ the emails mimic an actual Adobe email, telling the recipient that they have ‘a pending document’ which they are ‘required to access before the expiry date.’ It continues by informing recipients that ‘It’s mandatory you follow the below button.’
To improve engagement with the email, the subject line and the content of the email feature the recipients’ company and name.
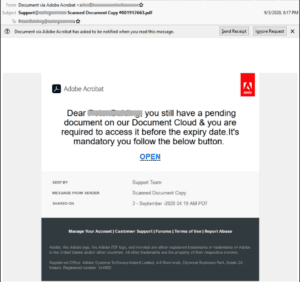
According to MailGuard, the cybercriminals behind the attack appear to be using read receipts to track who is actually opening the email, which is most likely being used to target specific addresses for future attacks.
The email says that it is coming from the Adobe Document Cloud but is actually coming from multiple compromised accounts in Bangladesh and India. The phishing page appears to be hosted using Google Cloud Storage. Google offers a free trial of this service to anyone with a Google account ($300 credit over 90 days) with the only restriction being a valid credit card.
If you receive an email like this delete it immediately and if possible, block the sender.
Zoom
As Zoom rises in popularity with businesses, so too does it with cybercriminals hoping to steal a user’s sensitive data.
Mailguard has found a new Zoom phishing scam and according to them, the email uses a display name of “Zoom IP”, along with the date. However, the email address in the “from:” field doesn’t use a domain belonging to Zoom. The email actually originates from an Amazon SES account. Its subject is simply the date and time.
The email is short and to the point, and addresses recipients using their email address. It informs recipients that they have received a video conferencing invitation, with a link provided to review it. The email ends with “Best, Team Zoom”.

According to MailGuard, unsuspecting recipients who click on the email are led to a fake Microsoft-branded login page and asked to “sign in to Zoom with your Microsoft 365 account”. Interestingly, this page is not hosted either on a Zoom or a Microsoft domain, but on what appears to be a compromised Oracle Cloud hosting account.
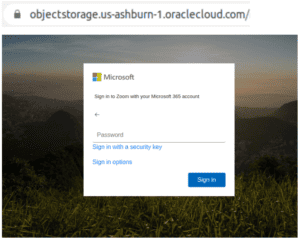
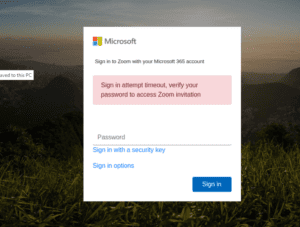
After entering your password and clicking on “Sign in”, the victim is then led to an error message saying “sign in attempt timeout”, at which point the scammers now have the scam victim’s login details to Microsoft 365.
If you receive an email like this, delete it immediately and if possible, block the sender.
Take Home Message
Email scams or phishing come in various forms either telling someone they’ve won money; their account has been hacked or a change in password.
This is another example of how the cybercriminals are taking advantage of the way we have adapted our communication behavior during the COVID-19 outbreak. With Zoom being one of the most popular video conferencing platforms we are using, the scammers are using emails tailored to Zoom to take advantage of our vulnerabilities.
If you’ve received an email from a sender that doesn’t seem familiar or a contact has sent you an email with information that doesn’t seem quite right, please flag it with us and we will review it for you.
Every month we will be sharing the latest in email scams courtesy of MailGuard.
To get a more comprehensive understanding of how to spot scam, please refer to one of our previous blogs:
Phishing – Think Before You Click!
Using mail protection software is a great way to control email, and reduce the chance of receiving such scam.
Contact Us
If you are interested in using MailGuard to add an extra layer of security to your email, reach out to us today at security@bangitsolutions.com or call us on 1300 770 035.

